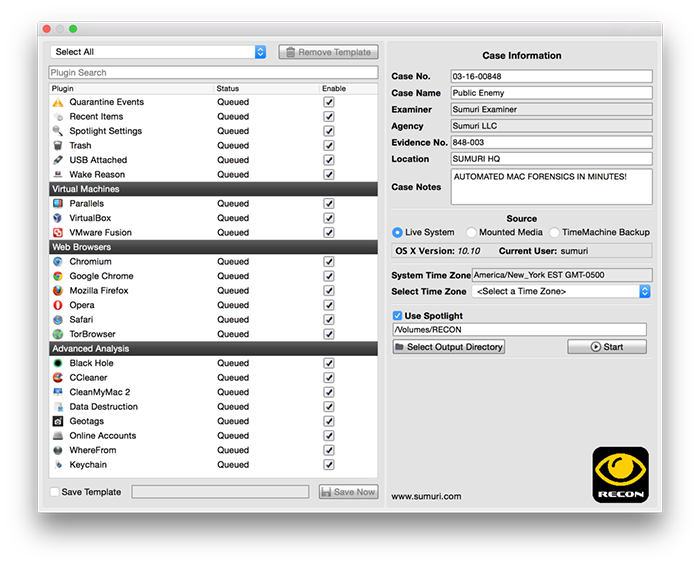
Credence Security - See the evidence that is missed by other forensic tools … Come join our Forensic Fundamentals Webinar Series on Mac Forensics Best Practices and Introduction to SUMURI's RECON Solutions.

W07_Lab4_msiddiq3.docx - Mohammad Siddiqui IT4853 \u2013 Computer Forensics Professor Scotland Assignment 4 \u2013 Case Project 7.1 Case Description Research | Course Hero