GitHub - meiersi/scyther-proof: A tool for the automatic generation of Isabelle/HOL correctness proofs for security protocols.
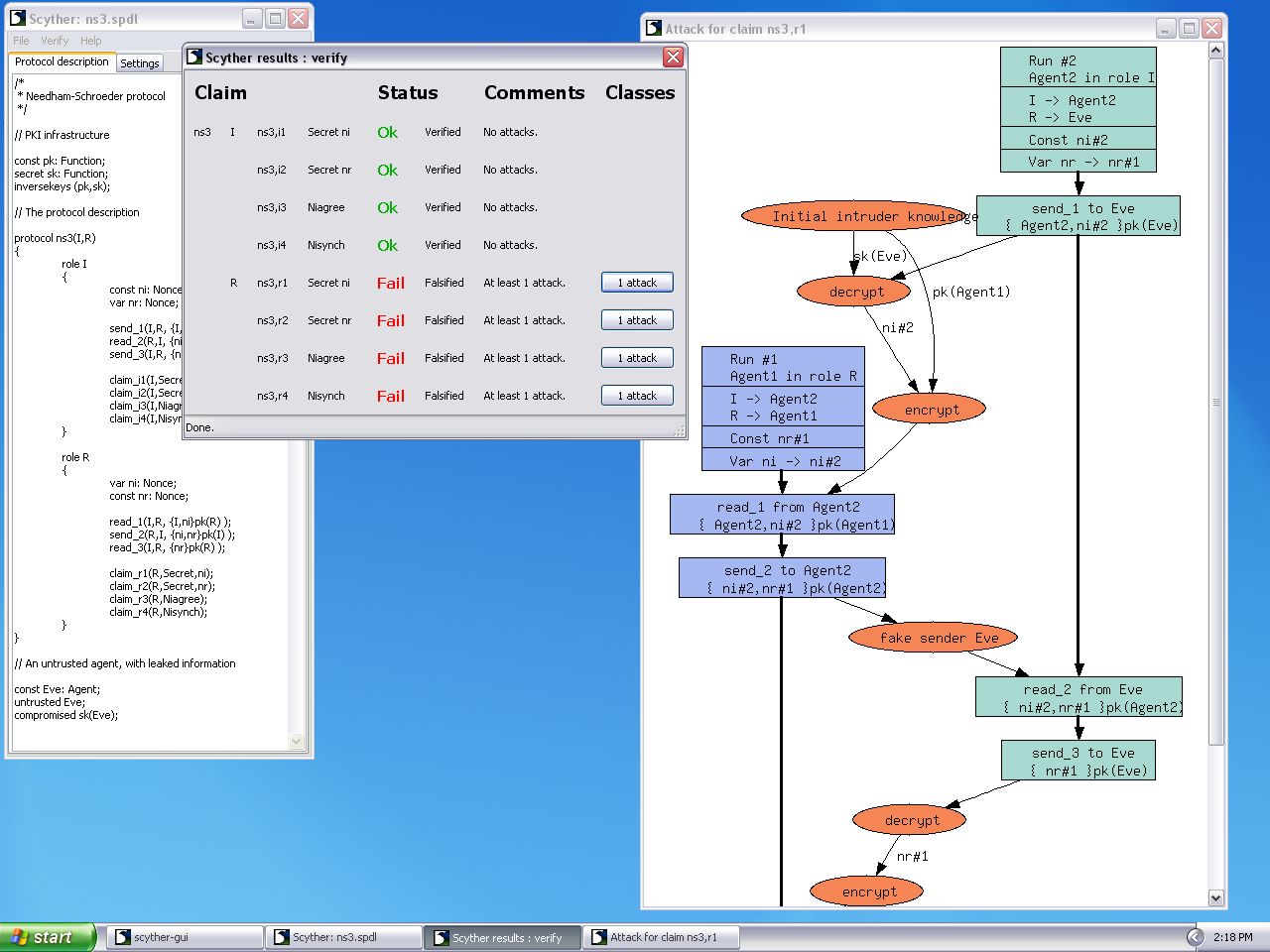
![PDF] The Scyther Tool: Verification, Falsification, and Analysis of Security Protocols | Semantic Scholar PDF] The Scyther Tool: Verification, Falsification, and Analysis of Security Protocols | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/3e8a202085b8b28e914db02ccc22201dc77dc968/2-Figure1-1.png)
PDF] The Scyther Tool: Verification, Falsification, and Analysis of Security Protocols | Semantic Scholar

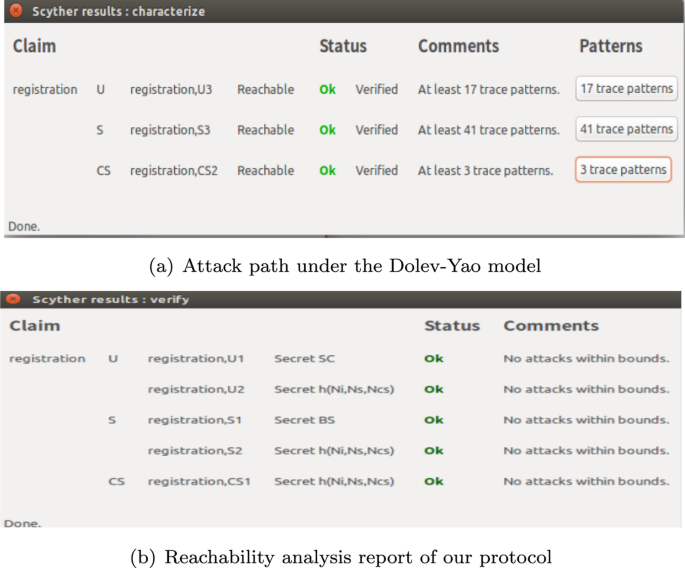
Mathematics | Free Full-Text | BCmECC: A Lightweight Blockchain-Based Authentication and Key Agreement Protocol for Internet of Things | HTML
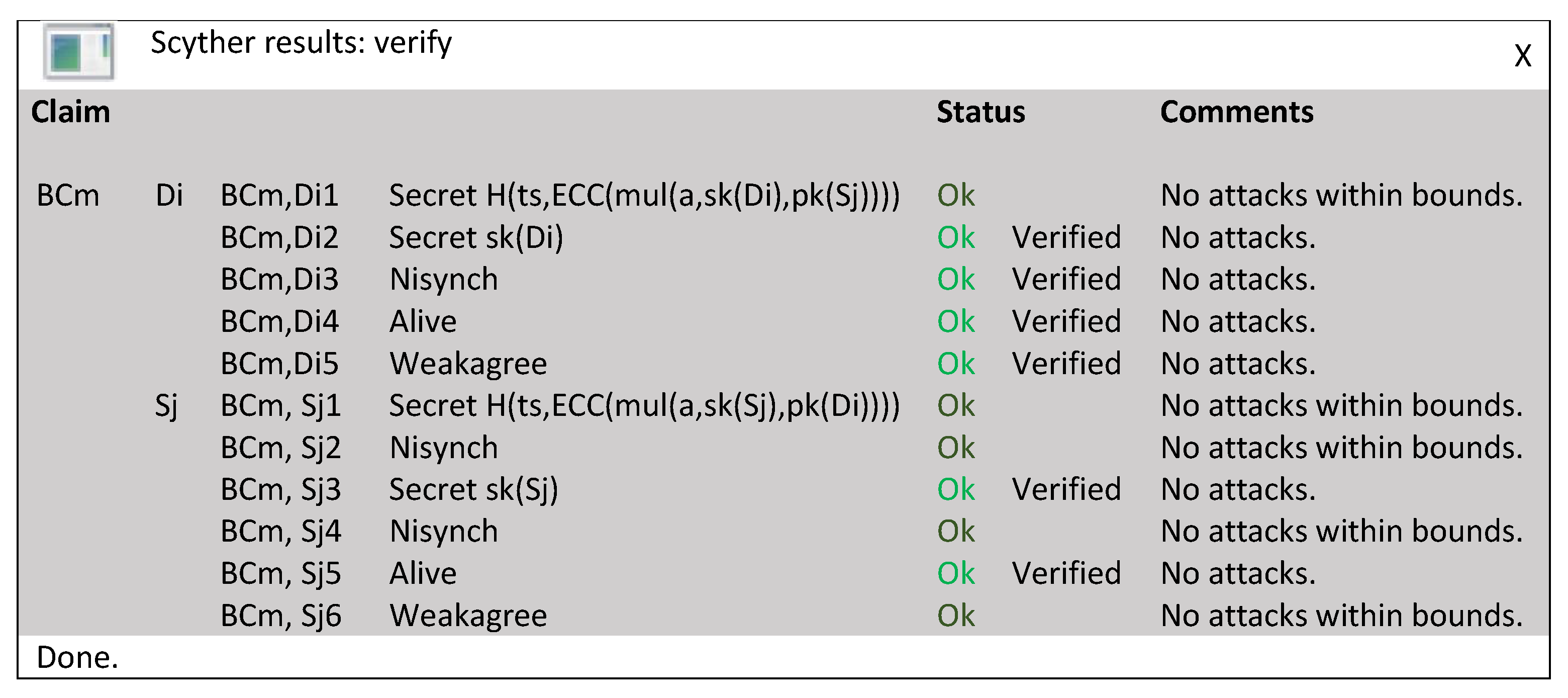
An efficient authentication and key agreement protocol for IoT-enabled devices in distributed cloud computing architecture | EURASIP Journal on Wireless Communications and Networking | Full Text
Mathematics | Free Full-Text | BCmECC: A Lightweight Blockchain-Based Authentication and Key Agreement Protocol for Internet of Things | HTML

Analysis and improvement of the Internet‐Draft IKEv3 protocol - Cheng - 2017 - International Journal of Communication Systems - Wiley Online Library

A secure end‐to‐end SMS‐based mobile banking protocol - Bojjagani - 2017 - International Journal of Communication Systems - Wiley Online Library

An enhanced anonymity resilience security protocol for vehicular ad-hoc network with Scyther simulation - ScienceDirect
GitHub - dvisionlab/Scyther: Curvilinear multiplanar reformat for Dicom Images, powered by VTK with python binding.

Sensors | Free Full-Text | Authentication Protocol for Cloud Databases Using Blockchain Mechanism | HTML

An enhanced anonymity resilience security protocol for vehicular ad-hoc network with Scyther simulation - ScienceDirect