
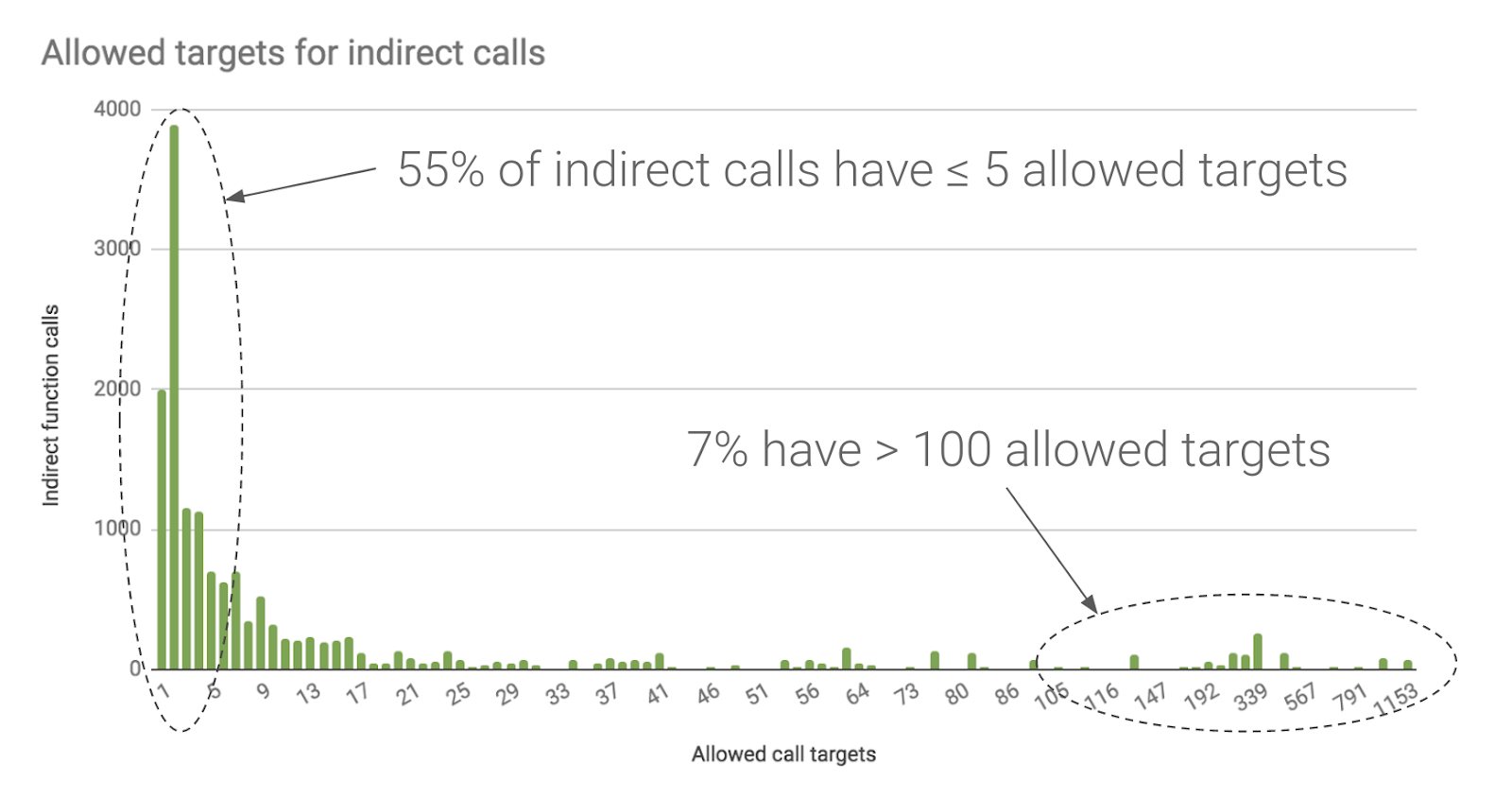
CDF of legal indirect callsite targets enforced by TypeArmor's CFI and... | Download Scientific Diagram
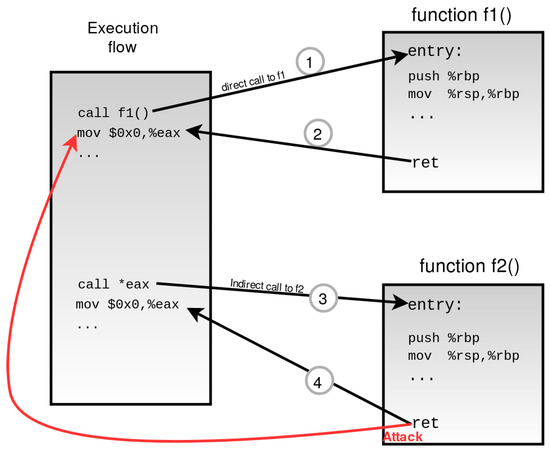
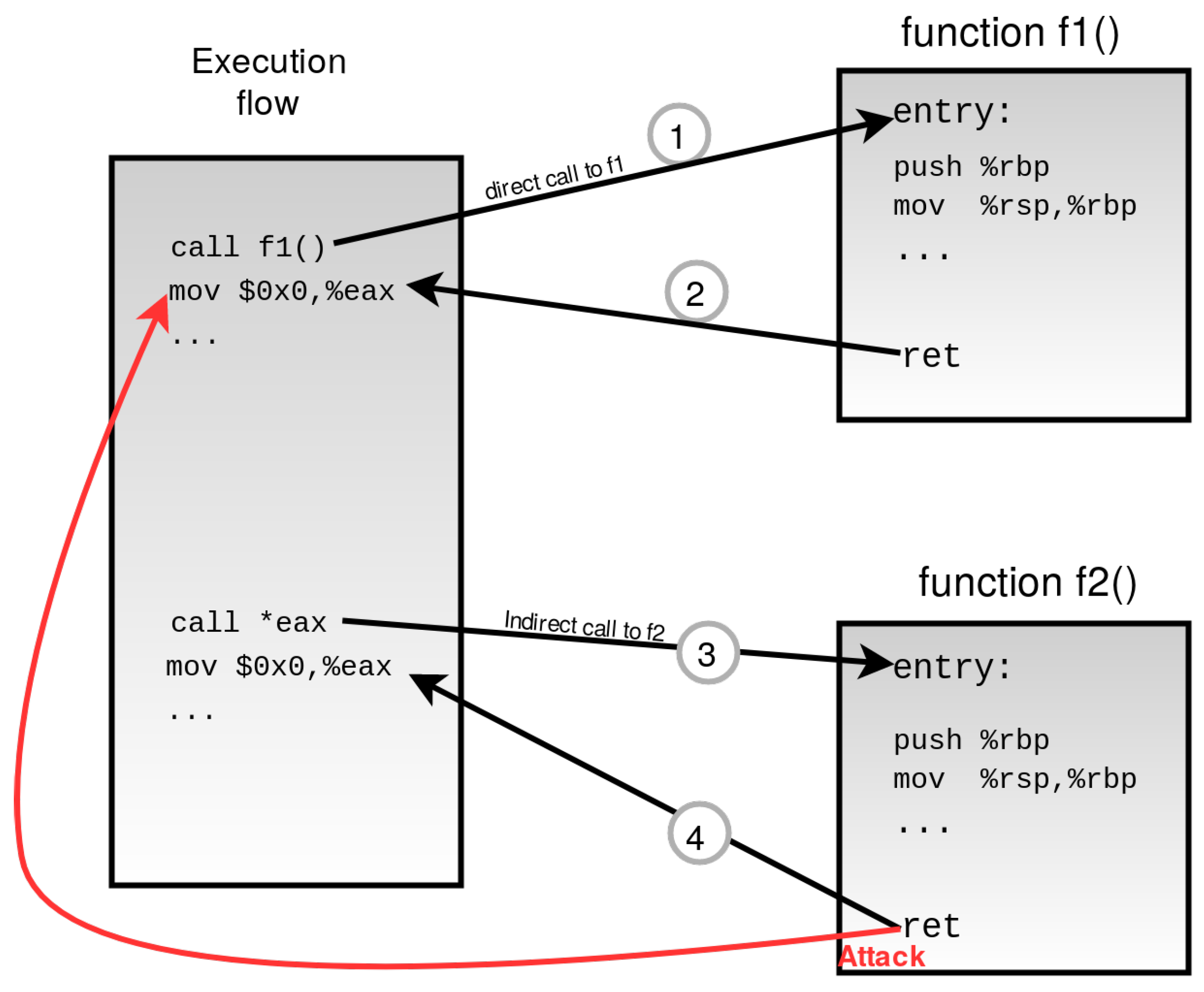
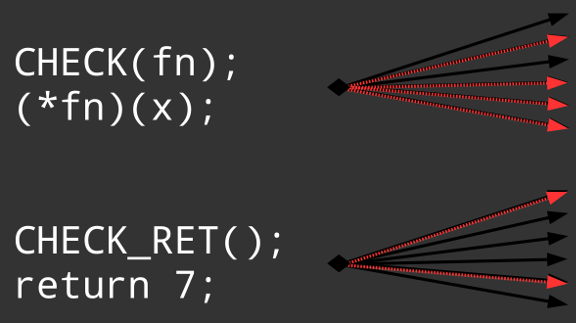
Fine-grained CFI approach bypass example. The attacker can successfully... | Download Scientific Diagram

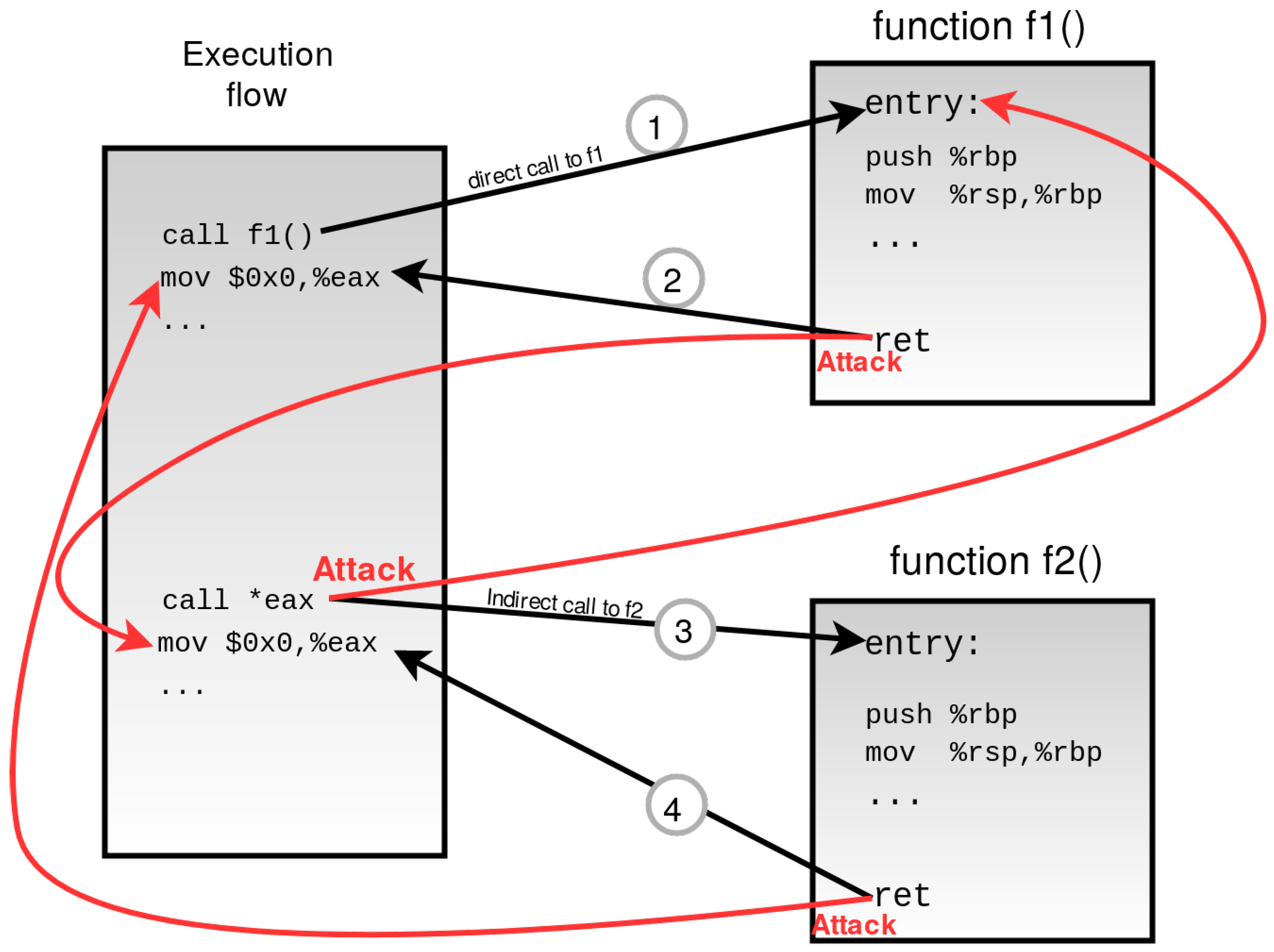
Fine-grained CFI approach bypass example. The attacker can successfully... | Download Scientific Diagram








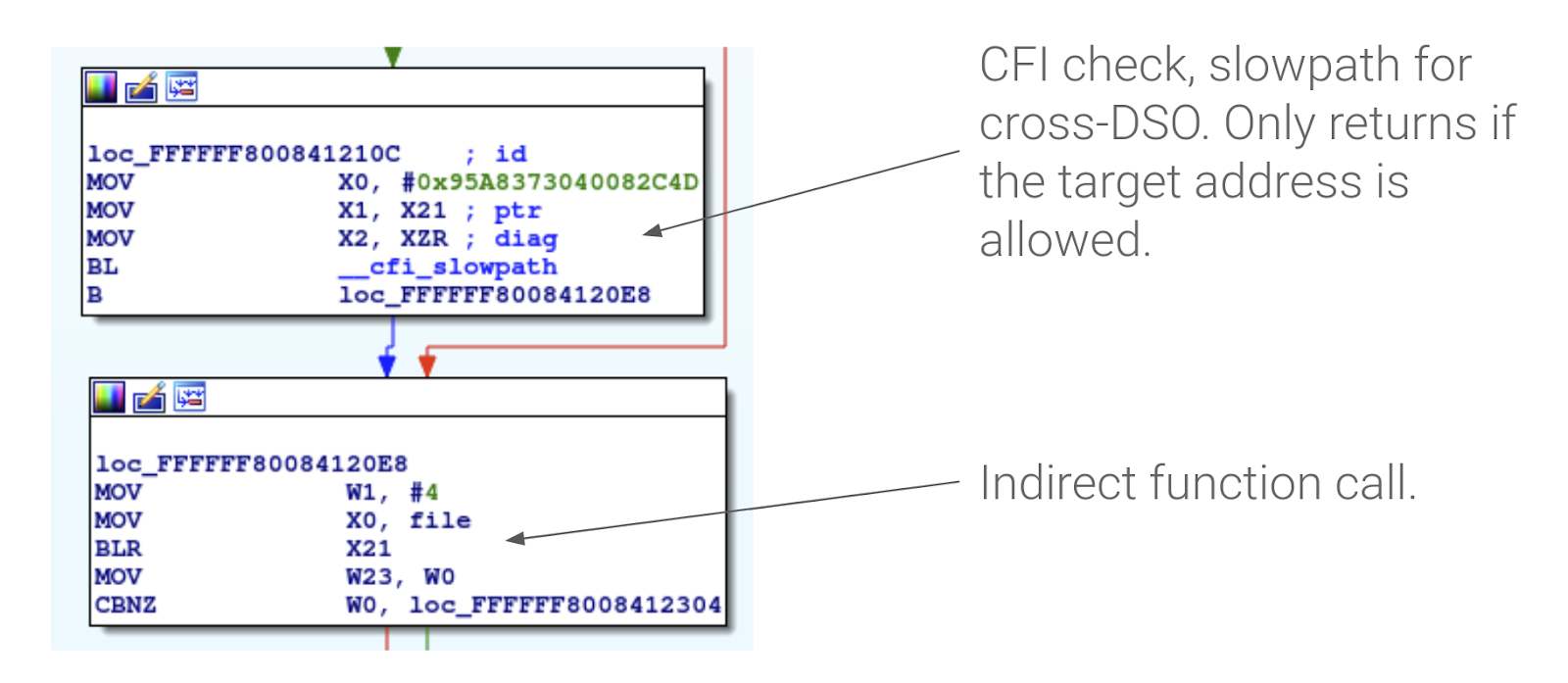
![PDF] Control-Flow Integrity: Attacks and Protections | Semantic Scholar PDF] Control-Flow Integrity: Attacks and Protections | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/6de5ef68d88aa26db023d3bfa2579f5f1e13891e/18-Figure3-1.png)
![PDF] Automated Multi-architectural Discovery of CFI-Resistant Code Gadgets | Semantic Scholar PDF] Automated Multi-architectural Discovery of CFI-Resistant Code Gadgets | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/9cf8d8ebe9a59d8605fa1ecf5872fb886fdc4b38/7-Table1-1.png)

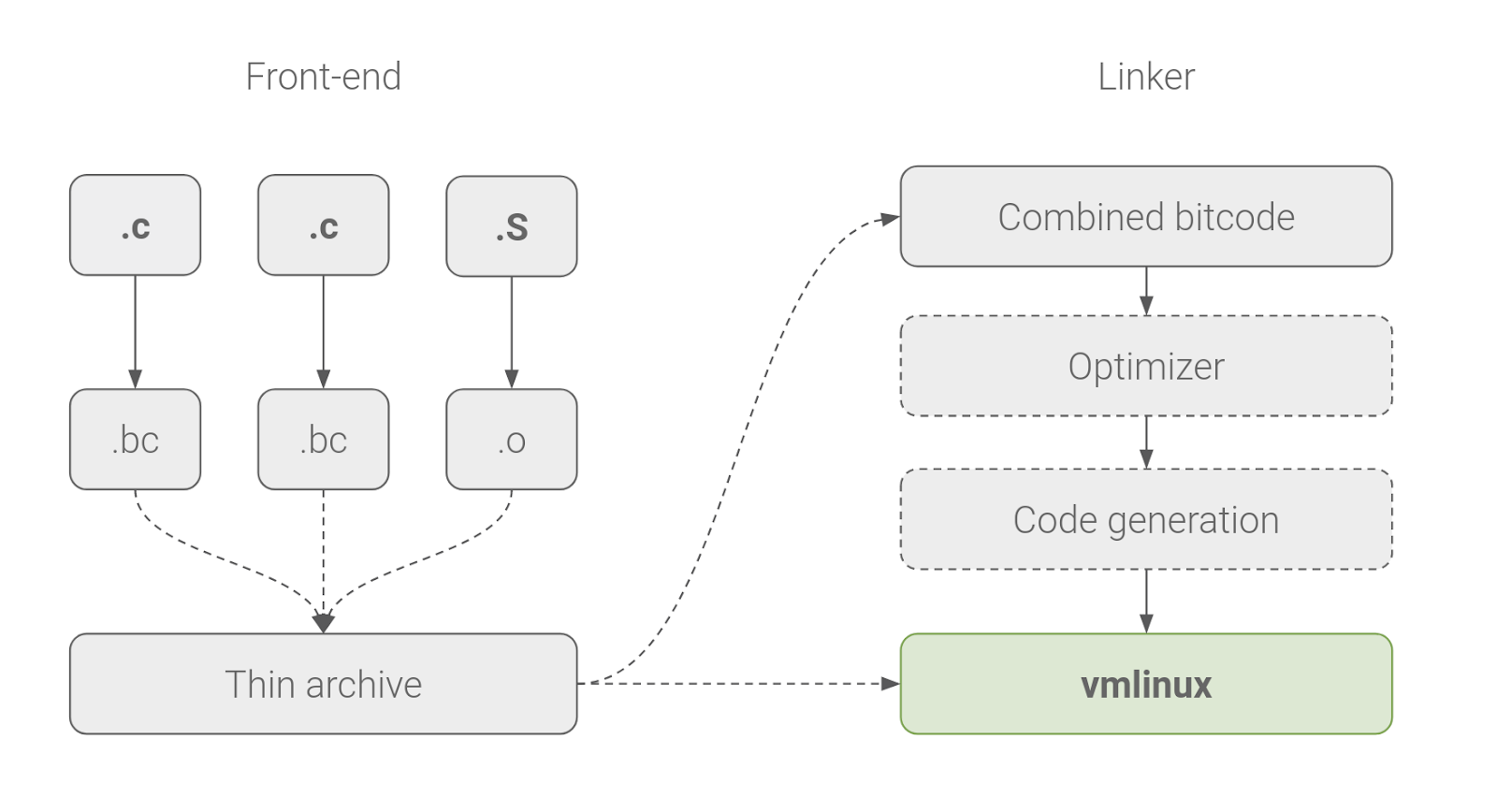
![PDF] Modular control-flow integrity | Semantic Scholar PDF] Modular control-flow integrity | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/157153c5c5b3fb42bd4de60d2cd8380e7038a82b/2-Figure1-1.png)